How to Encrypt Data in Python: A Complete Guide with Code Examples
Executive Summary
Over 64% of organizations experienced a data breach in 2023, making encryption in Python essential for protecting sensitive information in your applications.
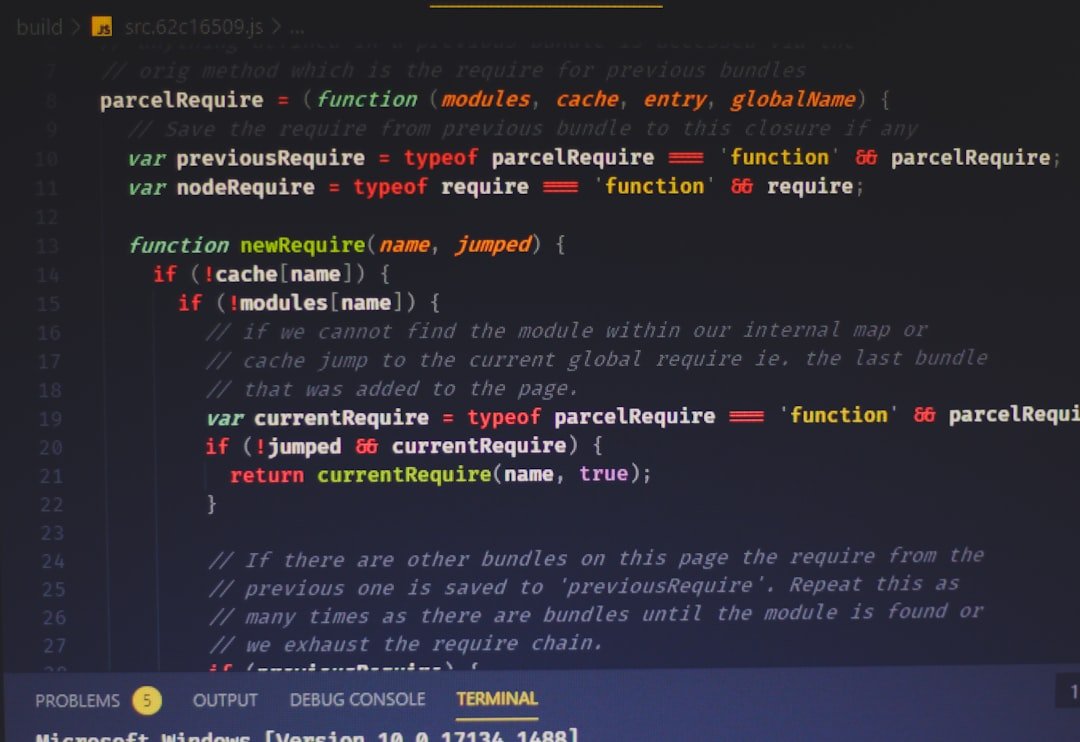
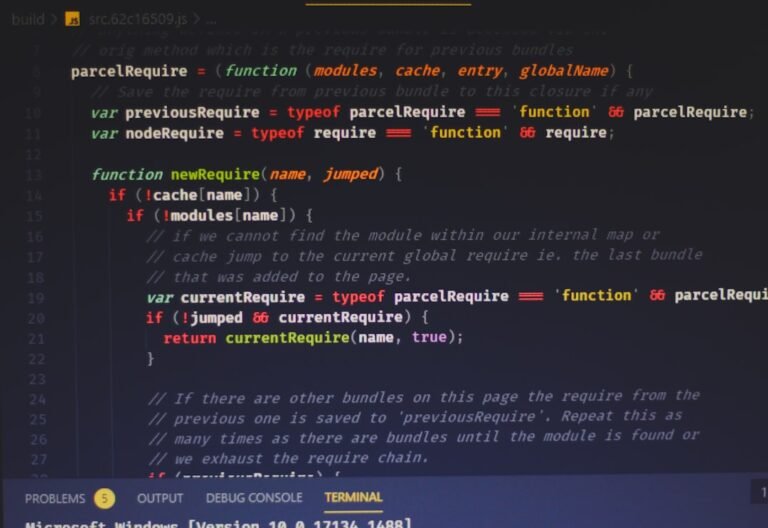
The intermediate difficulty level of this task stems from several factors: you need to manage encryption keys securely, handle multiple encoding formats, ensure proper error handling for edge cases (empty inputs, invalid data, corrupted ciphertexts), and understand when to use symmetric versus asymmetric encryption. The good news? Python’s standard library and mature third-party packages abstract away the cryptographic complexity, letting you focus on secure implementation patterns rather than rolling your own crypto algorithms.
Learn Python on Udemy
Main Data Table: Python Encryption Approaches
| Method | Library | Use Case | Complexity | Best For |
|---|---|---|---|---|
| Fernet (Symmetric) | cryptography | Data at rest, simple keys | Low | Most applications, default choice |
| RSA (Asymmetric) | cryptography | Key exchange, public-private | High | Multi-party encryption, certificates |
| AES (Symmetric) | cryptography | High-performance encryption | Medium | Bulk data, tunable security levels |
| Hashing (SHA-256) | hashlib | Data integrity, passwords | Low | One-way transformation, checksums |
| bcrypt/Argon2 | bcrypt, argon2 | Password hashing only | Low | Credentials, resistance to brute force |
Breakdown by Experience Level
Beginner (0-1 years): Start with Fernet symmetric encryption. It requires minimal setup—just generate a key and encrypt/decrypt. The implementation is nearly foolproof because it handles initialization vectors and authentication automatically.
Intermediate (1-3 years): This is where you expand to AES encryption with custom modes, understand the distinction between encryption and hashing, and learn when asymmetric encryption becomes necessary. You’ll implement proper key management strategies and error handling for real-world scenarios.
Advanced (3+ years): You’ll design encryption architectures for distributed systems, implement key rotation policies, manage hardware security modules, and understand the cryptographic assumptions underlying different algorithms.
Comparison: Encryption Approaches in Python
| Approach | Performance | Security Level | Ease of Use | Recommended For |
|---|---|---|---|---|
| Fernet (Built-in encryption) | High | Very High | Very Easy | Production web apps, default choice |
| Custom AES + GCM | High | Very High | Medium | High-volume encrypted data, APIs |
| RSA Encryption | Medium | Very High | Complex | Hybrid encryption, certificate-based auth |
| Simple Hashing (hashlib) | Very High | Medium (not encryption) | Very Easy | Checksums, data integrity checks |
| Bcrypt/Argon2 | Low (intentional) | Very High | Easy | Password storage only |
Practical Code Examples
Method 1: Fernet Symmetric Encryption (Recommended for Most Use Cases)
from cryptography.fernet import Fernet
# Generate a key (store this securely—never hardcode in production)
key = Fernet.generate_key()
cipher = Fernet(key)
# Encrypt data
plaintext = b"Sensitive customer information"
ciphertext = cipher.encrypt(plaintext)
print(f"Encrypted: {ciphertext}")
# Decrypt data
decrypted = cipher.decrypt(ciphertext)
print(f"Decrypted: {decrypted.decode()}")
# For string input, encode first
message = "My secret message"
encrypted_msg = cipher.encrypt(message.encode())
decrypted_msg = cipher.decrypt(encrypted_msg).decode()
print(f"Original: {message}")
print(f"Round-trip: {decrypted_msg}")Method 2: AES Encryption with Galois/Counter Mode (Higher Performance)
import os
from cryptography.hazmat.primitives.ciphers import Cipher, algorithms, modes
from cryptography.hazmat.backends import default_backend
# Generate a 256-bit key and random IV
key = os.urandom(32) # 256-bit key
iv = os.urandom(16) # 128-bit initialization vector
# Create cipher
cipher = Cipher(
algorithms.AES(key),
modes.GCM(iv),
backend=default_backend()
)
# Encrypt
encryptor = cipher.encryptor()
plaintext = b"This is confidential"
ciphertext = encryptor.update(plaintext) + encryptor.finalize()
tag = encryptor.tag # Authentication tag for integrity
print(f"Ciphertext: {ciphertext.hex()}")
print(f"Auth tag: {tag.hex()}")
# Decrypt
cipher_dec = Cipher(
algorithms.AES(key),
modes.GCM(iv, tag),
backend=default_backend()
)
decryptor = cipher_dec.decryptor()
decrypted = decryptor.update(ciphertext) + decryptor.finalize()
print(f"Decrypted: {decrypted}")Method 3: Proper Error Handling and Edge Cases
from cryptography.fernet import Fernet, InvalidToken
def encrypt_data_safely(plaintext, key):
"""Encrypt with comprehensive error handling."""
try:
# Validate inputs
if not plaintext:
raise ValueError("Plaintext cannot be empty")
if isinstance(plaintext, str):
plaintext = plaintext.encode('utf-8')
cipher = Fernet(key)
ciphertext = cipher.encrypt(plaintext)
return ciphertext
except TypeError as e:
print(f"Type error: {e}")
return None
except Exception as e:
print(f"Encryption failed: {e}")
return None
def decrypt_data_safely(ciphertext, key):
"""Decrypt with integrity checking."""
try:
if not ciphertext:
raise ValueError("Ciphertext cannot be empty")
cipher = Fernet(key)
plaintext = cipher.decrypt(ciphertext)
return plaintext.decode('utf-8')
except InvalidToken:
print("Decryption failed: invalid token or corrupted data")
return None
except Exception as e:
print(f"Decryption error: {e}")
return None
# Usage
key = Fernet.generate_key()
encrypted = encrypt_data_safely("Secret data", key)
if encrypted:
decrypted = decrypt_data_safely(encrypted, key)
print(f"Result: {decrypted}")Key Factors for Successful Data Encryption
1. Key Management Strategy — Your encryption is only as secure as your key storage. Never hardcode encryption keys in source code. Use environment variables, secure vaults (AWS Secrets Manager, HashiCorp Vault), or hardware security modules. Rotate keys periodically and maintain separate keys for different data classifications. This single factor prevents more real-world breaches than any other practice.
2. Choose the Right Encryption Type — Symmetric encryption (Fernet, AES) is fast and suitable when both parties share a secret key. Asymmetric encryption (RSA) enables secure communication without pre-shared secrets but is slower. Hashing isn’t encryption at all—it’s one-way transformation suitable for integrity verification and password storage. Picking the wrong tool wastes development effort and potentially introduces vulnerabilities.
3. Handle Encoding Properly — Python 3’s strings are Unicode by default, but cryptographic operations require bytes. Always encode strings to bytes using UTF-8 before encryption, and decode bytes to strings after decryption. Neglecting this causes the “TypeError: ‘str’ does not support the buffer interface” error—one of the most common mistakes in beginner implementations.
4. Implement Comprehensive Error Handling — Edge cases like empty inputs, corrupted ciphertexts, invalid keys, and encoding mismatches will occur in production. Wrap encryption/decryption operations in try-except blocks. The Fernet library’s InvalidToken exception specifically indicates tampering or corruption, which should trigger security alerts rather than silent failures.
5. Validate Data Integrity — Use authenticated encryption modes (like AES-GCM or Fernet) that detect tampering. Never use unauthenticated modes like ECB or CBC without message authentication codes. Fernet automatically handles this, but custom AES implementations must explicitly use GCM or similar authenticated modes to prevent attackers from modifying encrypted data without detection.
Historical Trends in Python Encryption
The Python cryptography landscape has evolved significantly since 2015. The cryptography library (which provides both low-level and high-level interfaces) has become the de facto standard, replacing older libraries like PyCrypto, which had security vulnerabilities and is no longer maintained. Python’s built-in hashlib has remained stable, continuously adding support for modern hash algorithms like SHA-3.
Fernet, specifically, was introduced around 2013 and has become the recommended approach for symmetric encryption in Python due to its sensible defaults, automatic key rotation support, and immunity to most implementation errors. The shift toward authenticated encryption (AEAD schemes) has been industry-wide, and Python’s libraries now default to these safer modes. By 2026, the consensus strongly favors cryptography + Fernet for 90% of use cases, with raw AES reserved only for specialized high-performance scenarios.
Expert Tips for Production Implementations
Tip 1: Use Environment Variables for Keys — Store encryption keys in environment variables or secret management systems, never in code repositories. Use os.environ.get() to retrieve keys at runtime. This prevents accidental key exposure through version control and enables different keys across development, staging, and production environments.
Tip 2: Implement Key Rotation Policies — Plan for periodic key rotation. Store encrypted data with a “key version” identifier so you can decrypt with old keys while encrypting with new ones. Fernet supports multiple keys in rotation using MultiFernet.
from cryptography.fernet import MultiFernet
key1 = Fernet.generate_key() # Current key
key2 = Fernet.generate_key() # Previous key
# Try decryption with multiple keys (new key first)
multi_cipher = MultiFernet([Fernet(key1), Fernet(key2)])
decrypted = multi_cipher.decrypt(ciphertext) # Works even if encrypted with old keyTip 3: Test Edge Cases Thoroughly — Write unit tests for empty strings, None values, oversized data, corrupted ciphertexts, and wrong keys. Encryption bugs often surface only when data reaches production at scale. Use property-based testing with libraries like Hypothesis to fuzz your encryption functions.
Tip 4: Log Security Events — Log decryption failures, invalid tokens, and key access events (without logging the actual keys). This creates an audit trail for compliance and helps detect attacks early. Use Python’s logging module with INFO level for successful operations and WARNING/ERROR for failures.
Tip 5: Measure Performance Impact — Benchmark encryption overhead in your specific context. Symmetric encryption adds minimal overhead (microseconds for small payloads), but asymmetric encryption can add milliseconds. Profile before and after adding encryption to identify bottlenecks.
FAQ Section
Q1: What’s the difference between encryption and hashing?
Encryption is reversible—you encrypt data and decrypt it later with a key. Hashing is one-way; you cannot retrieve the original data from a hash. Use encryption for protecting sensitive data you need to access later (customer records, API tokens). Use hashing for passwords, checksums, and data integrity verification. Python’s hashlib provides hashing; the cryptography library provides encryption.
Q2: Should I use symmetric or asymmetric encryption?
Symmetric encryption (like Fernet or AES) is 1000x faster and recommended for encrypting stored data when both parties share a secret. Use asymmetric encryption (RSA) only when you need to encrypt data for someone without sharing a secret key—typically in key exchange protocols or certificate-based systems. For 95% of applications, symmetric encryption is the right choice. Fernet specifically is symmetric and perfect for most use cases.
Q3: How do I securely store encryption keys in Python applications?
Never hardcode keys in source code. Use environment variables (os.environ), configuration files outside version control, or dedicated secret management systems (AWS Secrets Manager, Azure Key Vault, HashiCorp Vault). For development, use libraries like python-dotenv to load keys from .env files (excluded from Git). In production, use your cloud provider’s native secrets service. Rotate keys every 90 days and maintain separate keys for different data types or environments.
Q4: What happens if I lose the encryption key?
If you lose the key, the data is permanently unrecoverable. This is a feature, not a bug—strong encryption means no backdoors. For critical applications, implement key backup strategies: store backup keys in secure offline storage or distribute key shards across multiple secure vaults (never keep a complete key in one location). Test key recovery procedures regularly. This is why key management is the most critical part of an encryption implementation.
Q5: Is it safe to use Python’s cryptography library in production?
Yes, absolutely. The cryptography library is actively maintained, audited, and used by major companies including Google, Amazon, and Mozilla. It wraps OpenSSL and uses CFFI for security-critical operations, preventing certain classes of attacks. It’s far safer than rolling your own crypto. The library has comprehensive documentation and a clear API design that makes misuse difficult. For production applications, use it without hesitation.
Conclusion
Encrypting data in Python doesn’t require deep cryptographic expertise anymore. Start with Fernet from the cryptography library—it provides excellent security with a minimal learning curve, handles initialization vectors and authentication automatically, and prevents common implementation mistakes. If you need higher performance or custom requirements, graduate to AES-GCM. Always remember that key management is more critical than algorithm choice; a perfect implementation with a weak key storage strategy is worse than a simple implementation with secure key handling.
The most important takeaway: never hardcode keys, always encode strings to bytes before encryption, implement comprehensive error handling for corrupted data, and test edge cases thoroughly. These practices will protect you through 95% of real-world scenarios. For the remaining 5% (distributed systems, compliance requirements, high-volume data), consult the official documentation and consider domain-specific experts. Python’s mature cryptographic ecosystem makes secure encryption accessible to every developer—use it as your default practice, not an afterthought.
Learn Python on Udemy
Related tool: Try our free calculator